With the digital-first economy, small businesses are increasingly at risk from cyber-threats that can create chaos in their operations and expose sensitive information.
None of them are optional to Implement Essential Cybersecurity Solutions Every Small Business Needs now is an important step towards sustainable stability.
Whether it’s protecting networks or securing customer information, the right strategies help minimize risks and foster trust. In an ever-connected landscape of cybersecurity threats, a proactive stance keeps businesses strong, competitive and ready for new challenges.
Key Point
| Cybersecurity Solution | Key Point |
|---|---|
| Firewall Protection | Monitors and filters incoming and outgoing network traffic to block unauthorized access and prevent cyberattacks on business systems. |
| Antivirus & Anti-malware Software | Detects, prevents, and removes malicious software such as viruses, ransomware, and spyware from devices and networks. |
| Multi-Factor Authentication (MFA) | Adds an extra layer of security by requiring multiple verification methods, reducing the risk of unauthorized account access. |
| Data Encryption | Protects sensitive business data by converting it into unreadable code, ensuring information remains secure during storage and transmission. |
| Regular Data Backups | Ensures critical data is safely stored and can be restored quickly in case of data loss, ransomware attacks, or system failures. |
| Secure Wi-Fi Networks | Protects business networks with strong passwords, encryption, and hidden SSIDs to prevent unauthorized access. |
| Employee Cybersecurity Training | Educates staff on recognizing phishing, social engineering, and safe online practices to reduce human error risks. |
| Endpoint Security | Secures all devices like laptops, smartphones, and tablets connected to the network against potential threats and vulnerabilities. |
| Patch Management & Updates | Keeps software and systems up to date to fix security vulnerabilities and reduce exposure to cyber threats. |
| Access Control & User Permissions | Limits system access based on roles, ensuring employees only access the data necessary for their job responsibilities. |
1. Firewall Protection
Firewall is a basic level of protection which monitors the incoming and outgoing traffic based on defined security rules. It acts as a shield, protecting your internal systems from unauthorized access and nefarious attacks.

For small businesses, Essential Cybersecurity Solutions Every Small Business Needs – Firewall Protection make sure you are protected against hackers, malware and suspicious traffic.
Advanced features such as intrusion detection, real-time alerts, and application filtering are employed in modern firewalls. The business must implement hardware and software firewalls to establish sound rules, update the firewall regularly and keep optimally secure from increased cyber-attacks.
Why It Matters:
- Prevents unauthorized access to internal networks.
- Stops malware and cyberattacks from getting through the systems
- Monitors traffic in real time for suspicious activity.
- Prevents leaks of sensitive business information.
- Provides protection against outside threats.
How to Implement:
- Install hardware or software firewalls.
- Set custom security rules and filters
- Enable real-time monitoring and logging.
- Keep deploying new firewall firmware and configuration.
Pro Tips:
- Combine with intrusion detection/prevention systems.
- Restrict unused ports and services.
- Segment networks for better control.
- Review firewall logs frequently.
- Antivirus & Anti-malware Software
2. Antivirus & Anti-malware Software
Antivirus and anti-malware software are essential tools that protect your system from harmful programs, helping detect, prevent, and remove viruses, ransomware, spyware, trojans, and many other malicious threats.
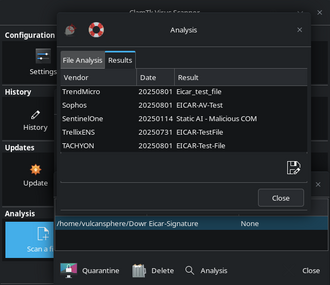
These tools constantly monitor the systems and offer real-time defense as per ever-changing threats. Essential Cybersecurity Solutions Every Small Business Needs – Antivirus & Anti-malware Software Advanced solutions incorporate behavioral analysis, automatic updates and cloud-based threat intelligence.
To protect against novel cyber threats that may emerge at any time and reduce the risks associated with it, small businesses must install reliable security software on all devices — regularly scan them and update their database consistently.
Why It Matters:
- Detects and removes malicious software.
- Defends against ransomware and spyware attacks.
- Protects against data corruption and system damage.
- Ensures safe browsing and downloads.
- Reduces downtime caused by infections.
How to Implement:
- The first preventive measure comes as install.
- Enable real-time protection features.
- Schedule regular system scans.
- Keep virus definitions updated automatically.
Pro Tips:
- Use cloud-based threat intelligence tools.
- Avoid free or unreliable software.
- Scan external drives before use.
- Monitor alerts and act immediately.
3. Multi-Factor Authentication (MFA)
MFA improves security by needing users to confirm their identity in two or more ways, from passwords and OTPs as well as biometric verification. This lowers the risk become of unauthorized access dramatically even when a password is compromised.

External authentication options — such as Essential Cybersecurity Solutions Every Small Business Needs – Multi-Factor Authentication (MFA) help prevent the compromise of sensitive accounts, be it email, banking or administrative.
Implementing MFA can take the form of an authenticator app or SMS-based codes. MFA should be enforced on all key platforms, preventing the use of compromised credenials that do not have additional verification layers.
Why It Matters:
- Adds extra security beyond passwords.
- Blocks unwanted attempts even where passwords are compromised
- Secures important accounts and sensitive systems.
- Reduces risk of phishing attacks.
- Strengthens overall identity security.
How to Implement:
- Use MFA (2FA) on all of your important accounts.
- Use authenticator apps or OTP enabler systems.
- The first ones that you should apply MFA to are admin and financial accounts.
- Integrate MFA with business platforms.
Pro Tips:
- SMS based MFA must be avoided.
- Use biometric authentication where possible.
- Educate users on MFA importance.
- Regularly review authentication settings.
4. Data Encryption
Data encryption: A process of transforming sensitive information into code that is unreadable by anyone not authorized to access it when transmitted or stored. It guarantees that intercepted data can not be misused as long as the keys necessary for decryption are safely stored.
Essential Cybersecurity Solutions Every Small Business Needs – Data EncryptionData encryption is crucial for securing customer data, financial records, and sensitive business information.

Business data implementation identifiers You can use encryption protocols like SSL/TLS for websites and secure storage solutions for internal data.
For the secure storage of both data at rest and in transit, encryption provides another layer of protection whilst also helping to meet compliance targets for data protection laws and industry standards.
Why It Matters:
- Secures confidential information from unauthorized access.
- Encrypts the data at the time of transfer and at rest.
- Prevents from compromising on data protection compliance.
- Prevents misuse of stolen information.
- Creates trust between customers and partners.
How to Implement:
- Use SSL/TLS certificates for websites.
- Encrypt databases and storage systems.
- Secure communication channels (email, messaging).
- Implement encryption tools for devices.
Pro Tips:
- Enable encryption of data both at rest and in transit.
- Use strong encryption standards (AES-256).
- Manage encryption keys securely.
- Regularly audit encryption practices.
5. Regular Data Backups
Backup frequently means copying necessary company data and saving it securely to try to redeem in the event of loss, cyberattacks or equipment breakdowns. This requires taking support measures for business continuity and disaster recovery planning.
In short, following up on the guide line Must Have Cybersecurity Solutions Every Small Business Should Consider – Regular Data Backups secures ransomware attacks as well as data loss due to accidental deletion.

Small businesses must automate of backup, be cloud base and always operate using 3-2-1 (For every data you have, to back up it must be stored three times in different locations) Performing regular backup restoration tests to ensure data integrity and recovery time.
A potent backup strategy reduces interruptions and mitigates huge economic and operational losses in the event of unforeseen accidents.
Why It Matters:
- Ensures data recovery after cyberattacks.
- Protects against accidental deletion.
- Minimizes downtime during failures.
- Supports disaster recovery planning.
- Prevents permanent data loss.
How to Implement:
- Automate regular backup processes.
- Set your backup on cloud and offline storage solutions
- Schedule backups daily or weekly.
- Test backup restoration regularly.
Pro Tips:
- Follow the 3-2-1 backup rule.
- Store backups in secure locations.
- Encrypt backup data.
- Isolate backup systems from primary networks.
6. Secure Wi-Fi Networks
To prevent unauthorized access and keep business data safe from cyber threats, secure Wi-Fi networks are critical. Hackers can easily break into systems that utilize weak or unsecured networks.

Using Essential Cybersecurity Solutions Every Small Business Needs – Secure Wi-Fi Networks will guarantee encrypted communication and access only to authorized personnel. Strong passwords, WPA3 or better encryption, disabling SSIDs.
Creating separate guest networks and regularly updating router firmware also help lower risk. Monitoring network activity and limiting access helps ensure additional protection, ensuring that only authorized users can safely connect to the business network.
Why It Matters:
- Prevents unauthorized network access.
- Protects sensitive business communications.
- Decreased risk of being hacked through vulnerable networks.
- Secures connected devices and systems.
- Maintains privacy of internal operations.
How to Implement:
- Use strong, unique passwords.
- Enable WPA3 encryption.
- Set up separate guest networks.
- Update router firmware regularly.
Pro Tips:
- Hide SSID for added security.
- Limit device connections.
- Monitor network activity.
- Disable unused network features.
7. Employee Cybersecurity Training
Employee cybersecurity training is a course that explains to employees how to be safe on the internet, what threats they should look out for, and how to handle sensitive or confidential information. One of the main causes for breaches in security is human error, hence training needs to be ensured.

Adding Essential Cybersecurity Solutions Every Small Business Needs – Employee Cybersecurity Training, for example, will train employees to identify phishing attempts and avoid malicious links while practicing good protocol. Because awareness and preparedness is improved through regular workshops, simulated attacks, and updated training materials.
Businesses need to establish explicit security guidelines and promote a culture of vigilance. Enlightened employees are the first line of defense against cyber attacks and mitigate enterprise risk dramatically.
Why It Matters:
- Reduces human-related security risks.
- Helps identify phishing and scams.
- Promotes safe online behavior.
- Protects company data from misuse.
- Strengthens overall security culture.
How to Implement:
- Conduct regular training sessions.
- Use phishing simulation exercises.
- Provide updated learning materials.
- Establish clear security policies.
Pro Tips:
- Make training ongoing, not one-time.
- Use real-world examples.
- Reward secure behavior.
- Test employee awareness regularly.
8. Endpoint Security
Endpoint security guards against cyber threats to any device connected with a business network, including laptops, tablets, smartphones and desktops. Looks like all of these gadgets are among the entry points for attackers if unguarded.

Implementing Essential Cybersecurity Solutions: All Small Businesses Should Have – endpoint security solutions ensures that all endpoints are tracked and protected with advanced tools such as endpoint detection and response (EDR).
Companies must ensure that security policies are implemented on devices, install protective software and enable remote management. Endpoint security is enhanced by routine updates and access controls designed to minimize vulnerabilities while maintaining secure operations on all connected devices.
Why It Matters:
- Cleanses all the connected devices against threats
- Prevents unauthorized access through endpoints.
- Secures remote work environments.
- Detects suspicious device activity.
- Reduces risk of data breaches.
How to Implement:
- Deploy endpoint protection tools (EDR).
- Enforce device security policies.
- Set up antivirus software on all devices.
- Enable remote monitoring and control.
Pro Tips:
- Set up remote wipe for lost devices.
- Restrict use of personal devices.
- Keep devices updated.
- Monitor endpoint activity continuously.
9. Patch Management & Updates
Regularly updating software, applications, and operating systems to address vulnerabilities and enhance security is known as patch management. Legacy systems are hackers’ honeypots: they have well-known vulnerabilities, making them easy to target for cyberattacks.

Password cracking is a big issue and one of the very first steps in the breach such as brute force attacks are used to find weak credentials, henceImportance of Essence Cyber Security Solutions All Small Businesses Must Have – Patch Management & Updates keep security holes closed sooner. Enable automatic updates, watch for patch releases and prioritize critical ones.
Keeping an orderly update regimen limits exposure to threats and helps improve system performance. Regular patching also helps reduce cyber risks, ensures compliance with security standards and goes a long way to improve overall operational efficiency.
Why It Matters:
- Fixes known security vulnerabilities.
- Prevents exploitation by hackers.
- Improves system performance and stability.
- Ensures compliance with security standards.
- Reduces risk of cyberattacks.
How to Implement:
- Enable automatic software updates.
- Track vendor patch releases.
- Prioritize critical updates.
- Maintain an update schedule.
Pro Tips:
- Test patches before deployment.
- Update all systems, including plugins.
- Remove outdated software.
- Document update processes.
10. Control of Access & User Permissions
Access control and user permissions restrict employees to the data and systems needed for their roles. This greatly reduces the risk of internal breaches and accidental data exposure.
How So Us 10 Cybersecurity Solutions Every Small Business Needs – Capabilities Businesses can implement role-based access control (RBAC) and highly enforce users’ authentication policies by using Essential Cybersecurity Solutions Every Small Business Needs – Access Control & User Permissions.
Conducting periodic reviews of user access can also catch and eliminate unused permissions. Restricting admin rights and tracking the login behavior also helps in strengthening it. Indeed, protecting sensitive information and ensuring accountability within the organization is vital.
Why It Matters:
- Limits access to sensitive data.
- Reduces insider threats.
- Prevents accidental data exposure.
- Enhances accountability among users.
- Protects critical business systems.
How to Implement:
- Use role-based access control (RBAC).
- Assign Permissions as per Job roles
- Regularly audit user access.
- Remove unnecessary privileges.
Pro Tips:
- Implement the principle of least privilege.
- Monitor user activity logs.
- Revise access permissions during job transitions.
- Use strong authentication methods.
Common Cybersecurity Mistakes to Avoid
Ignoring Software Updates
Neglecting software updates makes systems susceptible to known security vulnerabilities. Because hackers can easily exploit outdated applications, help ensure strong protection by regularly updating operating systems, plugins and software.
Using Weak Passwords
Weak or reused passwords open the door for unauthorized access. Easily guessable or crackable passwords require you to have strong, unique passwords for each account.
Not Enabling Multi-Factor Authentication
Risk is not ripe for the picking — turning off multi-factor authentication will only increase it. Without MFA, a compromised password may still gain access, making adding an extra verification for any important account essential.
Lack of Employee Training
Cybersecurity awareness training helps employees recognize threats, whether it be a deceptive email or an illegitimate message. Without an effective cybersecurity awareness program, human errors often risk sensitive data and compromise the entire business security system.
No Regular Data Backups
Failing to back up data regularly may lead to permanent data being lost during cyberattacks or system failures. Backups are crucial for rapid restoration and supporting business continuity in the face of unforeseen events.
Using Unsecured Wi-Fi Networks
Connecting to unsecured Wi-Fi networks can make sensitive information vulnerable to hackers. If proper encryption and security measures are not in place, attackers can intercept communications and gain access to business systems without authorization.
Ignoring Access Controls
Open access to sensitive data heightens the exposure risks of internal breaches. Access control helps protect sensitive data by allowing employees to access only the information they need, limiting opportunities for mishandling or inadvertent exposure.
Not Monitoring Network Activity
Unless you are monitoring what is going on your network, it becomes nearly impossible to be aware of any suspicious activity taking place. The focus is often on prevention, but without visibility, the threats could be ongoing and even lead to major damage before it can be stopped.
Using Outdated Security Tools
Security tools that have been in place for years only provide a stale defense against the contemporary cyber threat landscape. But advances in attack specialize, so effectively improving cyber security software and systems is very important.
Lack of Incident Response Plan
Lack of incident response plan delays cyberattack recovery A well-defined strategy enables firms to react swiftly, reduce damage and get back to business as quickly as possible post-security breach.
Future Trends in Small Business Cybersecurity
AI-Powered Threat Detection
AI will boost cybersecurity, by detecting threats in real time. Systems driven by AI can analyze patterns, identify anomalies, and react quicker than classic tools which enhances the general security efficiency.
Zero Trust Security Model
No user or device is inherently trusted under zero trust security. Each access request is automatically validated, minimizing risk of unauthorized access and amplifying defenses across networks and systems.
Cloud-Based Security Solutions
This will lead to increased adoption of cloud security tools as they are cost-effective and scalable. Organizations are going to depend on cloud service providers for elite protection and also secure storage as well as threat monitoring in real-time.
Increased Use of Automation
Automation will simplify cybersecurity procedures such as threat identification, patching, and response. It decreases human errors, is time-saving, and is improving the speed at which possible dangers are dealt with in business environments.
Rise of Remote Work Security
As remote work rises, the need to secure devices and networks no longer confined to offices grows ever more important. Companies are going to spend money on VPNs, endpoint security and secure access tools to secure truly distributed workers.
Stronger Data Privacy Regulations
Businesses will face a new set of data protection laws and compliance demands by the government. To preserve the business reputation and avoid fines, small businesses need to implement better security practices.
Biometric Authentication Growth
Finger and facial recognition use underway to biometrically authenticate instead of passwords. It’s more secure and convenient, which helps companies minimize the risk of password attacks and unauthorized access.
Conclusion
Small businesses are an easy target for cybercriminals, especially when they have limited resources and awareness about security. By using critical cyber hygiene solutions like firewalls, identity and access management (IAM) with multi-factor authentication (MFA), data encryption and regular backups, it makes a breach less likely both in terms of cost and the insurance aspect.
Moreover, pairing specialized tools like artificial intelligence-powered threat detection with employee education establishes a strong proactive defense ecosystem.
However, as businesses also adapt to the rapidly changing landscape of cyber threats, those who invest in layered security elements, continuous updates and prepare for evolving strategies will ultimately find themselves much better positioned to safeguard their data while preserving customer trust and maintaining long-term operationality.
FAQ
Why are small businesses targeted by cyberattacks?
Small businesses are often targeted because they typically have weaker security systems and limited resources. Cybercriminals view them as easy entry points to access valuable data and financial information.
What is the most important cybersecurity solution for small businesses?
There is no single solution; a layered approach is most effective. Combining firewalls, antivirus software, MFA, and data backups provides comprehensive protection against a wide range of cyber threats.
How often should cybersecurity systems be updated?
Cybersecurity systems should be updated regularly, ideally automatically. Critical patches and updates should be applied immediately to prevent hackers from exploiting known vulnerabilities in outdated software.
Can small businesses afford strong cybersecurity protection?
Yes, many affordable and cloud-based cybersecurity solutions are available. Investing in security is cost-effective compared to the financial and reputational damage caused by cyberattacks or data breaches.
How does Multi-Factor Authentication (MFA) improve security?
MFA adds an extra verification step beyond passwords, making it much harder for attackers to gain access even if login credentials are stolen or compromised through phishing attacks.